A Glance at Azure Governance: 5 Areas to Focus on for Azure Adoption
When it comes to Azure adoption, you need to use different governance tools to achieve the best outcomes for your business. Here at N4Stack, we work with customers to focus on several areas of governance.
1. Management Groups and Subscriptions
Since Microsoft introduced the concept of management groups, the ability to group subscriptions together to apply policies and permissions across the board has been a god send.
The advice from Microsoft up until this point was always to minimise subscriptions deployed in Azure, as with each subscription came a management overhead of manually applying policies, permissions, monitoring and cost controls at each level.
Management groups follow a similar principal to Organisational Units (OUs) in Active Directory, in that similar subscriptions for either the development lifecycle environment or business area can be grouped together and managed at a higher level.
This reduces time required on operational tasks and gives a broad overview of things like cost management. Benefits such as allowing TCO (total cost of ownership) to become an easily understandable set of graphs (rather than a complex and manual spreadsheet) and ensuring security policies are applied across the board will ensure that cloud adoption is a breeze.
2. Azure Policies
Think of Azure Policies as Group Policies, but cloud native and much better.
Azure Policies are a compliance and security baseline feature within Azure that allows compliance at-scale within an organisation. They are a native tool and are integrated right into the portal to be consumed straight away.
So how do you decide which policies you should use or create, and where should you apply them?
Every business has risks associated with what they do, whether that be a security risk, a risk of exposure or even an internal policy or process that must be adhered to (we call this a business risk).
At N4Stack we run discovery workshops with our customers and focus on these areas to identify the risks that are important to the business. We then convert those risks into policies which can help to mitigate them.
3. Budgets and Cost Control
Let us bust a myth first: not every workload is cheaper to run in the cloud.
One of the biggest factors in companies moving their workloads back out of public cloud is cost.
It’s something we see every day and it usually happens when there is no control placed around this element of cloud during the initial adoption.
Typically, the first time you know about a big bill is when it lands on your doorstep in a brown envelope. (Ok, we know it’s all done by email now!)
Within Azure there is now a native option for cost management.
It’s a clear-to-read and informative dashboard that can be accessed at all levels and provides information that can be digested by both non-technical and technical stakeholders.
From my own personal experience, the best way to keep on top of costs (after designing your cloud project at high level) is to use the Azure pricing calculator to put together a rough idea of how much you think the project will cost overall.
You then have the option to set a budget either on the subscription or resource group that holds that project and set up alerting at certain percentage thresholds of that budget.
If you’ve hit 80% of that budget within the first two weeks of the month, then either the resources put into the calculator were wrong or the environment hasn’t been sized correctly during deployment.
Either way this gives you the option to address this early and within the first billing cycle of the project and not be hit with big, unexpected costs at the end of each month!
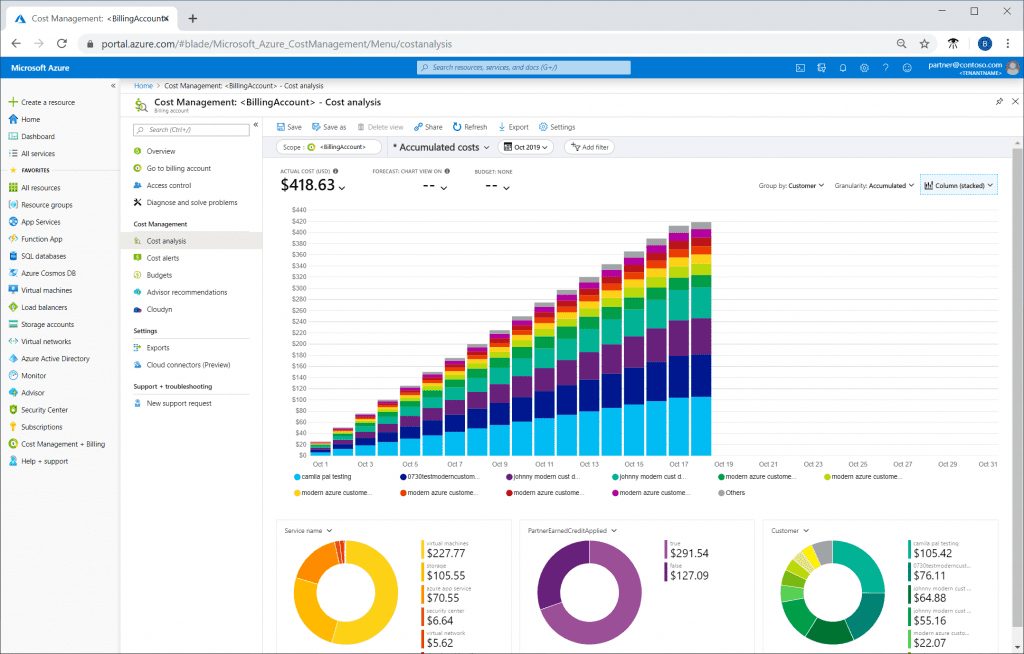
Azure Cost Management + Billing.
4. Role Based Access Control
Role Based Access Control (RBAC) is the security system that Microsoft essentially use to underpin the whole Azure platform.
It’s a next-generation identity management platform based around Azure Active Directory which creates identities and groups for users that can be used across the whole Azure platform.
Most resources within Azure tend to be split between two main areas of security focus: the management plane and the data plane. The recommended approach is to define permissions for each.
The management plane access should be given to the technical staff who are expected to look after the platform from the Azure perspective. These are not necessarily the same staff that would be expected to look after the data contained within a resource. By splitting out the access to these areas, you are protecting both your data and your staff.
5. Tagging
An Azure Tag is a key:value pair which is created and assigned to multiple resource groups or resources within Azure.
It’s important for visibility that a clear and concise tagging policy is defined when Azure is adopted within a company. Tags combined with a solid reporting structure will ensure that the lifecycle of resources is understood and managed, to keep costs down and orphaned project numbers vastly reduced.
During the discovery phase for defining a tagging policy, the areas to be considered include:
- Which project do the resources belong to?
- Which department will own the project?
- Which development lifecycle does the environment belong to?
- Does the project need to be re-charged to a department or cost centre?
- Who will support the environment?
These points can be used to determine the key:value pairs that suit the business and ensure that resources can be filtered, viewed and managed by the tags that they have attached to them.
Once this has been determined, it’s an easy process to bring the cost management data into an analysis platform like PowerBI and put together intricate reports to help determine costs of projects, departments, and support dependencies.
Are you ready to minimise risks, get control of your budgets, and accelerate your deployments? Get started with an Azure Governance Managed Service.
Further Insights
Azure Governance Managed Service
The Governance Managed Service sits at the heart of any operating model for Azure. Find out more about how the service lets you stay in control.
Got 2 minutes to spare to look at some Microsoft CAF videos?
Grab a coffee and take a look at our selection of short videos focused on Microsoft’s Cloud Adoption Framework (CAF).
How Not to Screw Up Your Move to Azure
A deep dive into our experience of delivering hundreds of cloud migration projects, including lessons learned and must-do activities.

Tim Rohde
Azure Platform Engineer
Tim has worked in the IT industry for over ten years, starting as a Helpdesk Analyst and working his way up through System Administrator and Infrastructure roles before specialising in public cloud and pursuing his ambition of automation and cloud adoption.
Find out more about Tim here.


